Our Products
Good Digital IDENTITY/KYC
Physical assets are rapidly being Digitized and Digital Assets are being accepted everywhere, exchanged with new business models and asset classes.
New technologies such as AI, Blockchain and Crypto are enabling these however lack Good Digital Identity, too many standards, and doesn't integrate well with the solutions that people are already familiar. Most of all aren’t secure.
Our solution uses an “ID Badge” that connects with multiple different platforms including dApps solving silos and and streamlines payments and services across all assets.
More importantly it based on the highest security available today leveraging FIPS-140-2 solutions, that no other software only based solution can match. To mitigate risks of security breaches advanced military grade technology to manage sensitive personal and private information.
Our platform is based on Mobile First, the default portal in today’s digital world to help enterprises, governments or a user build out their digital identity in an intuitive way with a role based security back-end console to help organisations mitigate operational risks.
Real-Time Good Digital Identity verification. Reduce dropout rates and cost of verification. Access AI, industry and proprietary data sources to help verify individuals seamlessly.
KYC Verification - Verify your users or very yourself
KYC Screening - Identify upfront PEP (Politically Exposed Persons (PEP), associates of a PEP, sanctioned, or other high risk persons
Ongoing Due Diligence - Keep verification up to date. Manages operational risks when renewing ID/KYC, such as when IDs expire. No more chasing customers for a valid ID if this is all done seamlessly on the user’s own smartphone.
Distribution and Processing - Manage costs and processing times by leveraging the module that is already enabled as part of the wallet, keeping everything digital.
Solution for existing users in organisations: Most digital ID solutions only cater for new users. What about existing users. We have a solution that solves for existing customers, seamlessly, securely and fast.
GDPR - Perhaps the most important and a clear differentiator to other Digital ID solutions is that our Good Digital Identity/KYC solution is designed for GDPR compliance. Organisations or individuals can confidently adopt our solution, knowing that they’ll be on the right side of Europe’s new consumer privacy laws.
Good Digital IDENTITY/KYC
(WHITE LABEL/OEM - Your BRAND LAUNCHED IN WEEKS not Months)
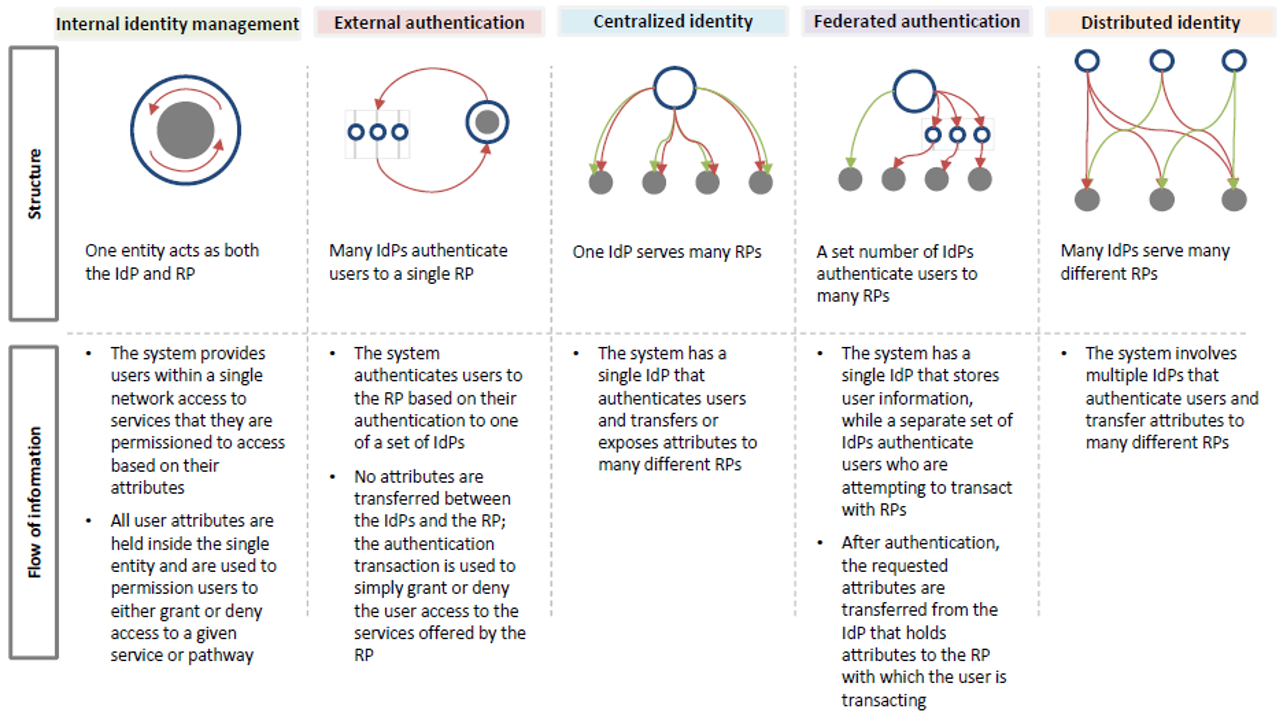
Shared Identity web of TRUST. Access credentials that and Individual can choose what to share. A modular, scaleble and secure product empowered on mobile
SECURE DIGITAL WALLET (PRIVACY USING UNQIUE BLOCKCHAIN TECHNOLOGY)
We make anything transactable, literally anything.
Secure Digital Wallet: A only Secure Digital Wallet in the world that leverages Miltary grade (FIPS140-2 certified chip) from which the user can transact; linked to the user’s digital identity for any network as well as securely delivering this via any mobile messaging platform e.g. WhatsApp, KaKao, Line, Messenger, WeChat etc.
Unstructured data and structured data verification: Currently most Digital ID solutions only cater for document verification which typically is based on structured data. Good Digital Identity solution caters for both and allows the ability to have unstructured data also to operate seamlessly and securely with structured data using blockchain.
Biometric, passwords, smart device verification: We believe as many organisation have already or will adopt different solutions, it it important to cater for multidimensional, consent-based, digitally verifiable identification, with a range of possible credentials and not be stuck with one standard and create further silos. This is why our solutions enable for Biometrics, Passwords as well as Smart devices seamlessly.
Blockchain: Our Product provides all the functionality needed by enterprise, governments or individual users building out their digital identity, and by dApp developers taking advantage of integrated payments and digital identity solutions.
In person verification: Good Digital Identity Solution also provide access to tradition forms of verification where existing organisations can adopt in person verification to operate seamlessly with traditional processes.
Digital Onboarding/Accredited Investor Platrform
(WHITE LABEL/OEM - Your BRAND LAUNCHED IN WEEKS not Months)
Solve your onboarding and operational compliance. Rapid onboarding, Securely and Digitally.
Accredited Investor Platform: Solve onbarding and User Acquisition. Why have your customers fill out so many forms. When you can onboard, distrubute, offer products and services real time with little or no friction.
Secure Digital WALLET Platform
(WHITE LABEL/OEM - Your BRAND LAUNCHED IN WEEKS not Months)
Identity and Messaging Protocols that form an inter-operable digital identity
API
Easy Integration to allow organisation or users to integrate immediately not months or years and benefit in the ability to adapt rapidly to the new digital economy.
API: Connects mobile users to their digital identity and allows private systems and businesses to plug into the Good Digital Identity ecosystem without uprooting their own architecture.
API
Rapid deployment and integration with existing solutions not just Blockchain
DatA and ANalytics
Integrated back-end console with intuitive Data and Analytics: Our Data and analytics solution allows organisation or users to seamlessly manage their associated data/resolvers from a single dashboard. Here one can manage multiple addresses, various dApps as well as seeing balances on key services.
Data and AnALYTICS
Intuitively and seamlessly manage data/resolvers from a single dashboard.
DECENTRALIZED CROSS PLATFORM Kit/SDK
Our platform allows users to securely store digital assets including Blockchain/Crypto Private Keys on the mobile device based on hardware. This helps mitigate centralized risks often found on exchanges. Rethink how to secure users. Custody Platform, Mobile Hardware Vault, Identify Server, based on a Cross Platform Mobile Development Kit that works across both iOS and Android platforms to address version and release management challenge.
DeCENTRALIZED CROSS PLATFORM KIT/SDK
Rapid deployment kit that covers any digital asset in a decentralized manner
Digital ID, much like other technological innovations such as nuclear energy and even the ubiquitous GPS, can be used to create value or inflict harm. Without proper controls, digital ID system administrators with nefarious aims, whether they work for private-sector firms or governments, would gain access to and control over data. History provides ugly examples of misuse of traditional identification programs, including tracking or persecuting ethnic and religious groups.
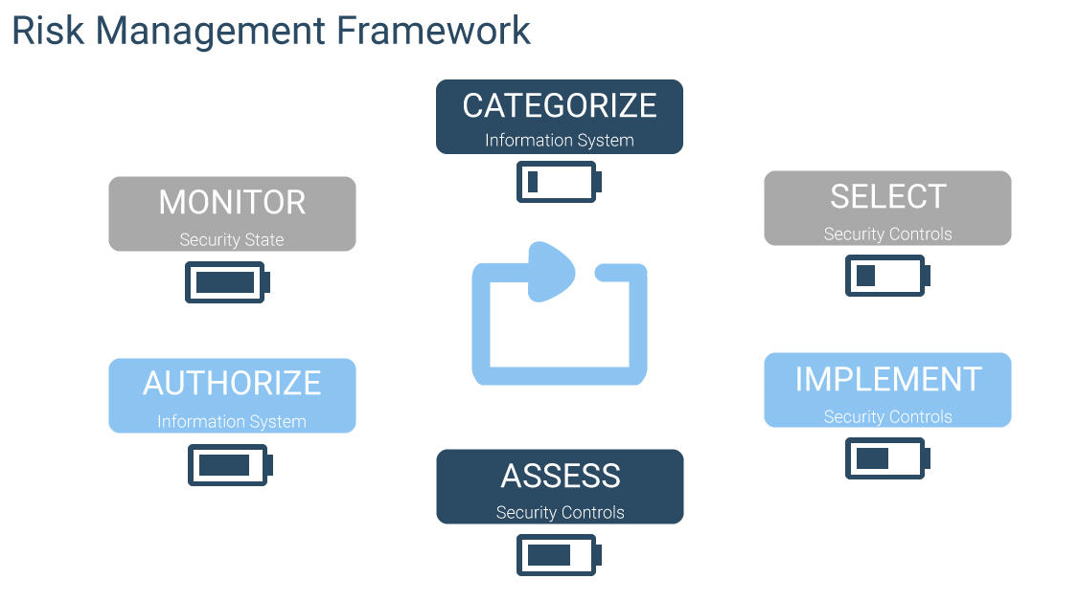
This is why our solutions not just look at technology by also managing RISK and leverage a well proven RISK MANAGEMENT FRAMEWORK not just technology to deliver INCLUSION, DESIGN and GOVERNANCE.